Ledger Login: A Detailed Guide to Accessing Your Ledger Wallet Securely
Introduction
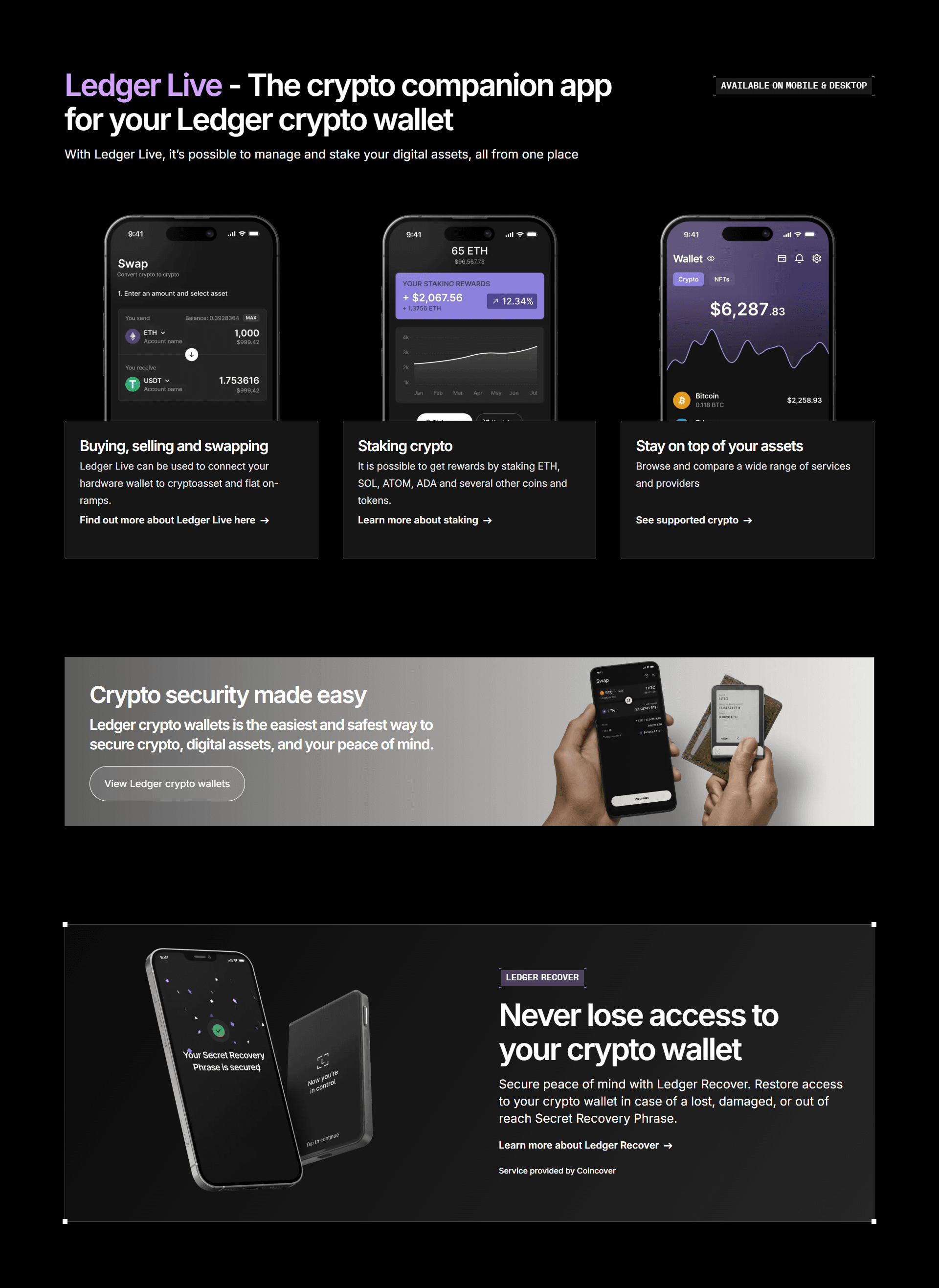
As interest in cryptocurrencies continues to grow, so does the need for strong security methods to protect digital assets. Ledger, a global leader in hardware wallet technology, provides a safe and dependable way to store private keys offline. To manage assets stored on a Ledger device, users rely on Ledger Login, a secure access process carried out through the Ledger Live application. Unlike traditional login systems that use passwords or online accounts, Ledger Login centers around physical hardware authentication, adding a powerful layer of protection for crypto users. This guide explains the purpose of Ledger Login, how it works, and the steps required to access your wallet safely.
Understanding Ledger Login
Ledger Login is the procedure used to connect a Ledger hardware wallet to the Ledger Live software. Instead of user credentials typed into a website, Ledger Login relies entirely on the following components:
A Ledger hardware wallet, such as the Nano S Plus, Nano X, or Ledger Stax
Your unique PIN code
The Ledger Live app on a computer or mobile device
Once these items are in place, Ledger Live can communicate with your hardware wallet, allowing you to interact with blockchain networks securely.
Why Ledger Uses Hardware-Based Login
The biggest security advantage of Ledger Login is that private keys never leave the physical device. Even if you log in using Ledger Live, your sensitive wallet information stays isolated from the internet. This design prevents:
Remote hacking
Unauthorized access from malware
Data leaks from compromised computers
Ledger Login is essentially a handshake between the app and a trusted hardware device, ensuring that only the rightful owner can approve actions.
How to Complete Ledger Login
Step 1: Install Ledger Live
Start by downloading Ledger Live from the official Ledger website. The software is available for:
Windows
macOS
Linux
iOS
Android
Avoid downloading Ledger Live from unofficial sources, as counterfeit versions may compromise your security.
Step 2: Connect Your Ledger Device
Attach your Ledger hardware wallet to your computer or smartphone. Nano X and Ledger Stax also allow Bluetooth connectivity for mobile use. Once connected, Ledger Live will search for the device automatically.
Step 3: Enter Your PIN
Your PIN is the first layer of security. Enter it directly on the device using its physical buttons. If the PIN is entered incorrectly too many times, the device resets to factory settings—an important feature to protect your assets if the device is stolen.
Step 4: Approve Ledger Live Access
Ledger Live will prompt you to confirm the connection. Approving this on the hardware device ensures that only someone with physical access can authorize the login.
Step 5: Access Your Ledger Dashboard
Once the device is verified, Ledger Login is complete. You will now see the Ledger Live dashboard, which provides access to:
Account balances
Transaction history
Crypto management tools
Staking options
App installation and updates
Every operation still requires confirmation on the hardware wallet, maintaining complete control over the security of your assets.
What You Can Do After Ledger Login
Manage Cryptocurrency Accounts
Ledger supports hundreds of digital assets. After logging in, you can add and organize multiple accounts, making it easy to track various coins and tokens in one place.
Send and Receive Transactions
You can send or receive funds safely using Ledger Live. Any outgoing transaction must be physically approved on your Ledger device. This prevents unauthorized transfers, even if your computer is compromised.
Install or Update Blockchain Apps
Each cryptocurrency requires its own app installed on the hardware wallet. Ledger Login grants access to these app management features so you can install, update, or remove apps as needed.
Stake and Earn Rewards
Ledger Live supports staking for various cryptocurrencies. After logging in, you can delegate your tokens, track rewards, and grow your portfolio—all while keeping your private keys offline.
Monitor Portfolio Performance
The portfolio section of Ledger Live provides real-time market data, value charts, and asset summaries, offering a complete view of your crypto holdings after logging in.
Troubleshooting Ledger Login Problems
Ledger Device Not Detected
Use a different USB cable
Try another USB port
Restart Ledger Live
Update the Ledger firmware
Incorrect PIN Attempts
Entering the wrong PIN multiple times triggers a security reset. If this happens, you can restore the wallet using your 24-word recovery phrase.
Bluetooth Issues
Move the device closer
Restart Bluetooth on mobile
Re-pair the device
Ledger Live Not Loading
Reinstall the application
Disable conflicting antivirus
Update your system software
Important Security Tips for Ledger Login
To keep your account safe, follow these best practices:
Never share your recovery phrase with anyone
Store your recovery words offline in a secure location
Only download Ledger Live from official sources
Keep your hardware wallet in a safe place when not in use
Verify transaction details on the device screen before confirming
Following these guidelines ensures you maintain full control over your assets.
Conclusion
Ledger Login provides a secure and reliable way to access your cryptocurrency through the Ledger Live application. By combining physical device verification, PIN protection, and offline private key storage, Ledger ensures that users maintain maximum control over their digital assets. Whether you are checking balances, performing transactions, staking tokens, or organizing accounts, the Ledger Login process allows you to manage everything confidently and safely. Understanding how this login system works is essential for anyone using a Ledger hardware wallet to protect their crypto investments.